“Sometimes I feel like…somebody’s watching me! And I have no privacy!”
(The Rockwell hit from…quite appropriately…1984.)
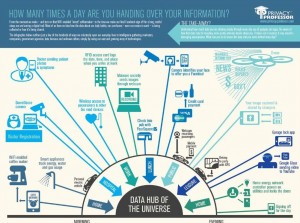
Each day, we are tracked by the ‘smart’ systems, mobile apps, personal communication devices and other surveillance platforms that have become commonplace in our daily lives. In an effort to educate more people, and businesses, about the data trails they are leaving behind (and the companies, data bureaus and marketers who are sniffing out that trail), I created this new infographic to show just a few of the many ways in which data is collected throughout a typical day within our omnipresent technology world…our “Internet of Things.”
Taken from http://www.privacyguidance.com/einfograph.html.
The infographic follows an average person as she wakes, visits a friend at the hospital, goes to work, leaves for lunch, spends the evening at a party, and then heads home. It portrays some of the many ways this average person unknowingly shares information about her whereabouts, habits, purchases and more.
Several examples of this data collection illustrated in the infographic include:
- Smart appliance vendors and utilities that learn what time a homeowner begins his day with a home-brewed cup of coffee or a 15-minute shower
- Hospital surveillance cameras capture visits, and doctors use wireless devices to control patient medical devices.
- Employer-issued RFID card tracks an employee’s every move while at work.
- Taxi- and street-view security cameras capture images.
- Mobile apps tied to video cameras and using facial recognition spot smartphone users and send coupons.
- Mobile payment devices process payments and share information with third-party marketing groups.
I recently spoke with NPR about this very topic, and coincidentally they just aired the radio report which talks about other types of daily collections of data that now occurs in everyday life. You can listen to it here.
How is privacy protected in such a brave new technology-based world? Or, how can it be? The danger is not necessarily in the collection of all that data; there can be some very beneficial things being done to make our lives better with data collected and analyzed. However, the concern is more often in the sharing and use of all that data. We welcome new ‘smart’ systems, mobile apps and personal communication devices into our lives because they promise to make our lives easier, save us money or connect us to our friends. What we don’t often realize is that most of these technologies are collecting data about us and then sending that data to an untold number of vendors, third-party partners and data bureaus. Big Data analytics are then used to gain insights into our lives in ways never before possible.
Categories of data collection
A big privacy challenge with the Internet of Things is that a huge amount of data is being collected, from so many different sources, and individuals are simply not being made aware of it all. Businesses that want to address privacy in a meaningful way need to think about how to deal with the unique privacy challenges within each of the following data collection categories:
- Individuals consciously providing their data to others. This is the most common way we have considered addressing data privacy throughout the years. Such as when individuals provide their personal information in exchange for an app, coupon, etc.
- Data collected automatically by apps and devices the individual uses. There are many of these, such as smart appliances, GPS apps, dieting apps, medical devices, and the list goes on and on.
- Situationally-aware devices in specific areas. For example, installing nanny-cams to record how people throughout your house is behaving; building security surveillance cameras; Internet cams focused on specific sites or locations; apps making posts based upon specific location parameters; etc.
- Pervasive surveillance. These include drones capturing everything in their general vicinity, dash cams capturing everything within their lens-shot, constant monitoring of online traffic, apps on phones capturing all conversations, wearable devices capturing everything in their area, and all other types of surveillance that capture basically everything going on wherever they are located.
How to Address?
All organizations that collect data from individuals, with or without their knowledge, need to follow an effective privacy management plan. Make the collection of data from devices and apps conspicuous and transparent.
So, in what ways can you make it known that data, and specifically what types of data, are being collected? It will often not be feasible to get consent from individuals to do such collection. But certainly in generally most all cases you can give some type of notice about the data being collected. Think beyond the traditional written (and usually long and generously peppered with confusing legalese) web site privacy notice. Some good possibilities include:
- Audible/spoken announcements.
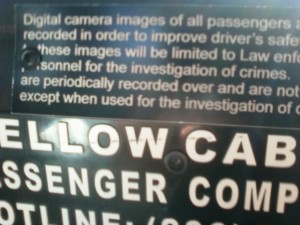
- Signs. This one was in the cab I took from SEATAC yesterday; it is actually pretty good:
- Videos.
- Banners on devices and apps.
- Symbols that each represents a different type of use (I really like this one).
- Privacy seals that can be clicked to get details of the associated privacy risks.
Think of more; use your imagination.
Security and privacy must work together to determine how to build privacy controls into all four categories of data collected, and must collaboratively address the following areas that overlap significantly between the two:
- Data Quality (Integrity, Accuracy): Monitoring and logging changes; endpoint validation; etc.
- Openness (Availability): Assigned responsibilities; documented policies and procedures; consistently applied non-compliance sanctions
- Use Limitations (Authorization, Access Controls): Determines the privacy impact of Big Data analysis on the associated data; implement privacy preserving analytics; etc.
- Disclosure Controls (3rd Party, Outsourcing, Selling): Ensuring safeguards continue to be applied
- Retention & Disposal: Keep data only as long as needed; irreversibly delete data at the end if the need
Bottom line for organizations of all sizes…
Data is being collected in more ways than ever before, from more devices and apps, and at a generally constant rate of speed. Much of this data can be associated with specific groups of individuals, and often to specific individuals themselves. If you are using or creating a device or app that collects data that relates to individuals, you need to build in information security and privacy controls.
Businesses creating all the apps and devices within this ever-evolving data-rich world must be aware of how the data they are collecting, analyzing and sharing impacts privacy. They must also know that full data lifecycle and where all the risks exist throughout. Appropriate safeguards (administrative, physical, technical) must then be implemented to reduce risks to acceptable levels.
This post was written as part of the IBM for Midsize Business (http://Goo.gl/t3fgW ) program, which provides midsize businesses with the tools, expertise and solutions they need to become engines of a smarter planet. I’ve been compensated to contribute to this program, but the opinions expressed in this post are my own and don’t necessarily represent IBM’s positions, strategies or opinions.
Tags: awareness, big data, breach, compliance, data protection, encrypt, encryption, IBM, Information Security, information technology, infosec, Internet of Things, IT security, midmarket, monitoring, NIST, non-compliance, NSA, personal information identifier, personal information item, PHI, PII, policies, privacy, privacy breach, privacy laws, privacy professor, privacyprof, Rebecca Herold, risk assessment, risk management, security, social network, surveillance, systems security, training